28.12.09
Best Online Virus Scanners
Most of these online security tools works great with continuous update of virus scan engines.
here I have listed some of Online virus scanners.
1. Virus Total
Virus Total is a free service that analyzes suspicious files and facilitates the quick detection of viruses, worms, trojans, and all kinds of malware.
The Main advantage of Virus Total is it scan a file using multiple virus scan rngines exists. So it can make an effective and thorough scan of files for viruses.
Virus total fetures:
Email Scan (scans your email attachments)
Hash Search (md5/sha1/sha256)
Use of multiple antivirus engines
Real-time automatic updates of virus signatures
Detailed results from each antivirus engine
Real time global statistics
2. Bitdefender Online Scanner
Online PC scanner. It scan the PC for malware, trojans and other threats and cleans PC.
Bitdefender's 60-Second QuickScan has following features
Very fast scanning. Less than 60 seconds
Runs online from any Internet connected PC
Doesn't slow down your PC
Based on award winning BitDefender anti-malware technologies
3. Mcafee Online Scanner
Mcafee online scanner is another online virus scan tool that detects threats on your PC.
4.Trend Micro House Call
To use this online scanner you need to install a small snippet on your browser.
8.11.09
Google Dashboard - a summery look of google products
This enables users to snap look at their all Google products within a compact view.
Google Dashboard provides information of Google account, contacts, blogs, Gmail email inbox-sent items list-spam, Picassa albums and other Google products you encountered.
Google blog says "Designed to be simple and useful, the Dashboard summarizes data for each product that you use (when signed in to your account) and provides you direct links to control your personal settings."
However still 19 Google services are not yet available on the Dashboard. These include Analytics, Checkout, AdSense, AdWords, Wave, App Engine, and Mobile, to name a few. These products recently available in the google dash board.
Google Dash Board
30.10.09
Speed up Windows 7 tweaks - Taskbar Thumbnail Preview
Step 01
Press WinKey+R, to run a program and type regedit to run Registry Editor.
Step 02
In the Windows Registry navigate to HKEY_CURRENT_USER\Control Panel\Mouse on the left hand side and after double click on MouseHoverTime in right hand side.
Step 03
In the 'Edit String' message box, enter the preferred delay at the 'Value data' field. You can set it as 10 or 0. then Click OK and exit the registry editor.
Please restart the computer to see the results.
2.9.09
How to remove Norton
Norton has also released some new versions recently, however newer products has that disadvantage of slowing your computer speed. Comparing to other Virus removal tools like kaspersky, Eset, BitDefender etc., Norton is uses huge memory in computer.
Most users finds that it's harder to completely remove Norton products from their computers with Norton's built-in uninstallers. However there is Norton removal tool that lets you remove Norton products from your PC if you wish to do so.
Download Norton removal tool
10.6.09
Registry hack to increase Start Menu loading time
Here is another registry hack that you can increase the Windows XP start menu loading time. This registry tweak may also be applied to Windows Vista and Windows 7.
Normally Windows takes a little time lag before jumping to menus and sub menus. But we can reduce this time lag and increase the Start Menu Showing time by modifying the registry entry.
This is the method to follow:
Click on Start > Run > then type regedit and hit Enter to open Registry Editor.
Expand the menus in Registry Editor as follows :
My Computer > HKEY_CURRENT_USER > Control Panel > Then Click on Desktop .
After click on Desktop, on the right side search for the key 'MenuShowDelay' Double click on it to modify the entry and change the value to '0'. After you done close the Registry editor and Restart Computer.
After restart of computer you can see the faster display of Start menu and other program menus.
1.6.09
Microsoft Live Search turned in to Bing
Microsoft says that the present Online search engine mostly delivers web pages that are not relevant to the content user looking for. (Yes this quote is almost true.)
Here what Microsoft says "Bing organizes search results so you can quickly and easily locate the content that matters most. And Bing helps you harness that information through exclusive tools specific to your key tasks, leading to more-informed decisions. Put simply, Bing is a first-of-its-kind decision engine." Behind Bling
It seems that Microsft's Bing is really attempting to provide the search content to point. Because now when you search for a term on the Bing, It displays the text content of the targeted page when you hover on each search result.
Microsoft targets to attract a good amount of present Google searches with their new technology and this seems Google have to face a some amount of competition in near future.
Bing Search Engine
Discover Bing
 |
25.5.09
Increase Gmail loading time

This is a good news for users who are with slow internet connection or dial up connections. Not only this is a useful feature if you don't want to load everything inside the Gmail and just want check the recent emails.
Gmail lab has developed a new feature that you can just preview latest 10 messages of the inbox.
You can not read the full message by clicking on each of them, it just preview the new messages of the Gmail Inbox.
How to enable the Feature :
Just follow the link to Enable this feature on Gmail lab section under Settings tab.
Then click on Inbox preview section to activate it.
However there are already several other tools which can enabling the quick preview of Gmail Inbox such as the Firefox extension 'Gmail Manager'. Go here for a complete list of Gmail tools and external applications .
You can view new developments of Gmail lab under the settings of Gmail.
24.5.09
Google Chrome 2.0 faster than Firefox ?
How to update to Chrome version 2.0 ?
Existing users don't want to download a new version. Instead just open the Chrome and Click on 'Tools' icon in the right side of the window and then click on 'About Google Chrome'. The About window lets you to automatically update to the new version.
Or if you are still not experienced the Chrome yet, Just go and Download it from Google Chrome Download Page.
New Developments in Version 2.0
Increased Stability : As they fixed about 300 bugs in the new version.
Form Autofill : Shows information that previously entered.
More Speed : 30% faster than the previous version. Users can play with Java scripts even with opening more tabs. So in some occasions I have getting faster download of web pages than with Firefox (Only my own experience)
Full Screen Mode: Hide the title bar and the rest of the browser window by hitting F11 key.
New Tab Page: It no more shows most visited web site thumbnails when you open a new tab.
Google Chrome team says they are focusing on much developments in future.
2.5.09
How to recover Windows XP passwords with PwDump and MdCrack
How many times did you attempted to recover the windows passwords lost bu you. ?
This guide will show you how to securely recover Windows Passwords using two tools PwDump and MdCrack.
Download two tools here (PwDump 7.1 and Mdcrack)
First of all I'll give a brief about what is MdCrack and Pwdump.
PwDump used to extract raw passwords from Windows SAM file. (In Windows OS, the SAM file is used to store all information about user passwords and logins) Once you extracted passwords from windows SAM file you can use them to find the what is the exact password.
You also can download PWdump from Andres Tarasco Acuna's web site here
The MdCrack part is converts raw hex data extracted by PwDump to decide the exact password. (MdCrack web site : http://mdcrack.openwall.net)
Ok let's begin to Recover our Windows Passwords.
Step 01:
First of all Download two tools here (PwDump 7.1 and Mdcrack)
Extract the zip and copy two folders to a main level directory in my computer (for ex: to D:\ drive)
Step 02:
Run Your CMD 'Command Prompt' in Windows
Start > Run > type 'cmd' > OK.
Step 03:
Now type the path to PwDump.exe in command prompt.
EX: D:\pwdump\pwdump.exe (don't put spaces between words)
then hit Enter to extract raw passwords from SAM file.
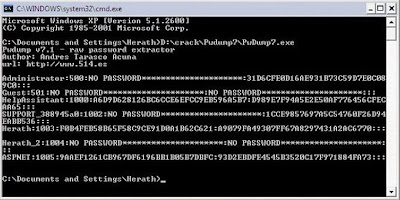
Here is how it looks like on my Windows PC. It should looks same in yours. (click on the image to get a larger version)
Step 04:
Now copy all raw data from command prompt(CMD) to a notepad and save.
(right click on CMD and click on mark to enable select and select the content of passwords and type CTRL+V to copy.)
Close the CMD.
Step 05:
Now again open the CMD and type the path to MDcrack to fire up MdCrack.
You should care in this step.
EX: D:\md-crack\MDCrack-sse.exe --algorithm=NTLM1 A9079FA49307FF67A8297431A2AC6770
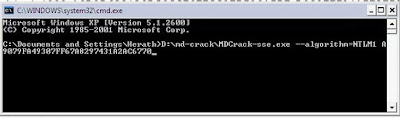
the hex part (A9079FA49307FF67A8297431A2AC6770) should be the second part of the hex data shown after each user. (after the : mark of hex raw)
Now hit enter to begin the process.
You are alsmost done and just wait till the MdCrack recovering the passwords.
Don't forgot to let us know your rresults here.
Happy Cracking/Recovering
1.5.09
How to add custom favicon in new Blogspot blogger
So most blog masters lost their favicons that previously enabled. Many blog owners have seen the classical blog icon again.
However there is a hack or a trick to enable custom favicons in blogspot blogs.
You have to move the url of the favicon between the Style (CSS) part and closing head tag.
Here is how to do it.
Login to dash board --> Layout --> Edit Html.
Now search for the code : ]]></b:skin>
then place the url to the blogger favicon right after the above code.
Here is how it should see after you finalize it.
]]></b:skin>
<link href='http://path to icon' rel='shortcut icon'/>
<link href='http://path to icon' rel='icon'/>
</head>
If you successfully done this, you should seen the blogger favicon in browser address bar.
27.4.09
Speed up Windows 7 - Applications, tweaks and tips
Download this Registry File. (adware, spyware tested, clean and malware free)
This file changes the values in windows 7 registry to make things work faster work faster, smoother and more stable. This is a small release and doesn't change much yet, but mostly makes folders work and load faster, increases internet and download speed and shows hidden and protected files, which, in most cases makes spotting unwanted files a lot easier.
Few more Windows 7 Tweaks to optimize and speed up.
1. Click on start
2. Search for Run
3. Typ: msconfig
4. Click on the tab Boot
5. Click on Advanced options...
6. Turn on Number of processors
7. And make your choose how many core u want use 2,4 or maybe 8
8. Click on OK
7. Apply
8. Reset your computer and next time computer will start up faster!
ReadeyBoot and ReadyBoost
ReadyBoot is a tool designed to analyze the boot processes and it allocates additional random access memory (RAM) to optimize the process. ReadyBoost is also available to the ReadyBoot feature when actual system RAM is in short supply. ReadyBoot will then pull the needed RAM from a USB 2.0 flash drive.
the second thing is simply use readyboot with a good clean usb stick, fastest way is to have the usb formatted as ntfs. also a tip, if you think you need the fast boot times and don't have a proper usb stick, pay close attention to read and write speeds when you buy one, a label "readyboost ready" doesn't make it a fast usb stick. values over 20MB/s make it a fast stick.
Free up the hard disk space by removing Kaspersky temporary files
Here is a great Windows tip to remove your unnecessary files stored by Kaspersky Internet Security and Kaspersky Anti Virus. You can save a huge amount of your hard drive space by applying this method.
Let's see how to do it in few steps.
01.
Enable “Show Hidden files and folders” option from the folder options of My Computer window.
02.
Disable the Kaspersky Security system.
Then open Kaspersky Application --> Settings --> Options then disable the Self -Defense by removing the mark of the check box.
03.
NowExit from the Kaspersky application ( KAV or KIS ).
Then Go to C:\Documents and Settings\All Users\Application Data\Kaspersky Lab\AVP8.
04.
Open the “Data” folder where you will see many files named as av1A.tmp, av2A.tmp..... etc. and with other files and folders.
05.
Then select all the files having a .tmp extension (Click on Search Button in the same window --> click on all files and folders --> type " *tmp " to search for all temporary files in that folder )
Then delete all the temporary files (.tmp files) you have selected. Make sure not to delete other files. You will now notice a high reduction in your disk space.
( You can do this automatically by downloading Ccleaner application. Ccleaner can increase your hard drive space by removing unwanted files from it. Just give a run on everyday and see how much of files it can remove.)
20.4.09
Wifi network Security - be secure at Wi-Fi hotspots
Free hotspots operate in two ways:
- Using an open public network is the easiest way to create a free HotSpot. All that is needed is a Wi-Fi router. Private users of wireless routers can turn off their authentication requirements, thus opening their connection, intentionally or not, for sharing by anyone in range. The disadvantage is that access to the router cannot be controlled.
- Closed public networks use a HotSpot Management System to control the HotSpot. This software runs on the router itself or an external computer. With this software, operators can authorize only specific users to access the Internet, and they often associate the free access to a menu or to a purchase limit. Operators are also now able to limit each user's available bandwidth - each user is therefore restricted to a certain speed to ensure that everyone gets a good quality service. Often this is done through Service Level Agreements.
The websites you are visiting exposed. While not necessarily a big deal to some, it’s only the tip of the iceberg.
· Login information to any unsecure (Non-SSL) site that you sign into. This can include but is not limited to banking and email, which can include a vast amount of personal information. Even sites such as web forums or a majority of social networking sites such as Twitter, MySpace, and Facebook are also available to hackers.
Using an unsecured hotspot or entering your password into an unsecured web site while on one is basically like leaving your front door unlocked where complete strangers can wander in and find any information about you.
A few key bits of information to keep in mind are:
· Never connect to an unsecured network. The various encryption settings for wireless networks are:
o Unsecure – No encryption at all. Anything broadcasted over the network can be seen by anyone.
o WEP Encrypted – The bare minimum of encryption and safety on wireless networks. Although it provides protection against random people, anyone that wants to break the encryption can do so easily in 5 minutes.
o WPA & WPA2 – the definite choice for security. Although they can be broken, information sent over these networks is encrypted and take much more to break.
· Only connect to crucial sites using HTTPS (You should see the lock symbol in your browser and also https://websiteyourarevisiting).
· Make sure your antivirus/malware software is up to date and running.
· Make sure your firewall is up and running.
· Make sure Windows is updated with all the latest security patches from Windows Update.
· Turn off file and printer sharing before connecting to public networks. Although you may not have sensitive files on your computer, there are still malicious attacks that can be launched with it on.
· If you do have sensitive files on your network and must connect to public hotspots, consider encrypting that data using a program such as True Crypt.
These are only a few key points to keep you safe while connecting to wireless hotspots. Basically when you are on them your need to be extra cautious of sites you visit and information you enter into your pc onto these sites.
18.4.09
How to enable show hidden files and folders disabled by viruses
Some times viruses and other malicious programs may not allowed or completely wipe out your hidden files and other private folders in C:\ such as hidden folders in 'Documents and Settings'.
Virus may block the access to those hidden files even you enable 'show hidden files and folders' by going to "Folder Options".
The virus implements a policy such as “Shockwave.dll” that’s forcing system to keep hidden files forever not visible or hidden.
Your virus guard may some times failed to block or quarantine those viruses. So the following guide will help you to enable the access to your hidden files and folders.
- Go to Start Menu and click on Run (Windows Vista and Windows 7 uses Start Search instead).
- Type RegEdit and press Enter to run Registry Editor.
- Navigate to the following registry key:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\
CurrentVersion\Explorer\Advanced\Folder\Hidden\SHOWALL - In the right pane, verify that the CheckedValue value data is REG_DWORD type. If it’s not (such as belongs to REG_SZ), then delete the CheckedValue value data.
- If CheckedValue has been delete, create a new DWORD (32-bit) Value and name it as CheckedValue.
- Double click on CheckedValue and change its value data to 1 (virus may change it to 0 or 2).
- Within the same registry key, verify that the Type value data is of REG_SZ type, and has the value data radio. If not, set it to radio. Virus may change it to blank.
- Set the system to show all hidden files and folders by going to Folder options, and then check if hidden files and folders are show.
19.3.09
Kaspersky Internet Security 2009 (8.0.0.506)
Kaspersky released it's new version of Kaspersky Internet Security 2009 or 8.0.0.506 version few days ago.
You can download the latest version of Kaspersky I.S. here.
http://www.kaspersky.com/kis_latest_versions
What's new in Kaspersky Internet Security 2009 ( 8.0.0.506 )
- Kaspersky Internet Security now requires considerably less input from the user, due to the use of lists of trusted applications (“white-lists”).
- New integrated system scanning before applications starts first time to prevent dangerous programs and penetrating the system.
- New Internet browser configuration to analyse the the security of browser side programs.
- System Restore wizard helps repair damage to your system arising from malware attacks.
- Monitors access to confidential data, user files and application folders.
- The new Privacy Cleaner wizard which erases from the user’s computer all information about his or her actions throughout the session.
- Upgraded updates of phising sites database.
- Integrated Wi-Fi connection scanner.
So most wise decision is activating the Kaspersky trial version and after it expired getting a working key from Kasperky lab which saves your time.
Global ranking for Anti Virus software as folows.
Rank 1 - Kaspersky Internet security
Rank 2 - Bitdefender
Rank 3 - Eset Nod 32
Rank 4 - AVG Security
Rank 5 - Macafee
Rank 6 - Norton
5.3.09
How to remove winguard.exe
Winguard.exe is created with Visual Basic 5. And It can only run on Win32 systems that have Msvbvm50.dll installed.
Winguard.exe can be removed by all free virus scanners including AVG, Avert Stinger and others such as Trojan Remover etc.
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
as value Windll=c:\winguard.exe.
1.3.09
Winguard Pro 2008 - Lock windows applications and programs
Here are some features of Winguard Pro.

- Lock Programs, Applications, EXE Files with a Password
- Encrypt Files, Folders and Entire Drives
- Disable Zip and Self Extracting Files
- Lock Windows at Boot and the Boot Keys (F8)
- Password Protect Windows Explorer
- Password Protect Web Browsers - Internet Explorer and FireFox.
- Disable Software Installation and Downloads.
2.2.09
Top 10 Windows Tools
I'll discusses here the tools needed for a perfectly running Windows system.
Some of these tools may freeware and some are shareware or licensed tools.
But all these tools have high performance and power to keep windows error free.
1. RegCure
my first choice is Regcure.It scans the whole registry and shows all errors.
You also has the option to view all start-up items of the computer and stop unneccesary items. I'm using it for a long time and is the best registry cleaner.
Regcure finds all junky items, which keeps intact by other tools such as norton,pc on point, and reg mechanic.
"RegCure™ provides fast and efficient scanning and cleaning of your registry so that your computer can run at an optimal level of performance. RegCure identifies invalid registry items and decides what items you want to remove. After removing registry entries, you have the option to restore your computer to a previous state."
Download "regcure" here
2. Trojan Remover
It also based on registry and scans all critical places for trojans and malwares.
Trojan Remover can detect some viruses left by popular virus scanners.
TR is designed specifically to disable/remove Malware without the user having to manually edit system files or the Registry. The program also removes the additional system modifications some Malware carries out which are ignored by standard antivirus and trojan scanners.
Trojan Remover scans ALL the files loaded at boot time for Adware, Spyware, Remote Access Trojans, Internet Worms and other malware. Trojan Remover also checks to see if Windows loads Files/Services which are hidden by Rootkit techniques and warns you if it finds any.
Download Trojan remover
3. CCleaner.
Registry optimizer and removes unnessary files from system.
CCleaner scans all places for unnecessary files .
It has the ability to detect errors of the registry and scan the computer for unnessary files.
also to view startup objects and stop them.
It's uninstaller is a worthy tool which shows items that does not removed by 'add or remove' program
Download 'CCleaner" here
4. Spybot
My another favorite is 'SpyBot Search and Destroy'.
Once my system infected with the trojan called 'Virtumonde', I take up with all popular virus scanners like Kaspersky and PC tools to remove virtumonde. None of them was able to remove Virtumonde but Spybot did it superbly.
Spy bot is an uncomparrable tool to remove
all malware, adware and also it removes viruses.
You can detect and remove some threats which does not remove by some giant virus scanners such as kaspersky.
It also featured with a file shredder and other useful tools.
Download "spybot" here
5.Power Quest Partition Magic.
You don't need any other tool to manupulate your disks and partiotions, if you have Partiotion Magic software.you can quickly and easily create partitions, which act as "file drawers," on your hard disks for storing valuable information such as data files, applications, and operating systems.
Storing information in separate partitions helps you organize and protect your data, safely run multiple operating systems, and reclaim wasted disk space.
PartitionMagic enables you to secure your data by physically separating it from other files. Separate partitions also make backups to networks and removable drives easy.
You also able to create rescue disks with PM.
Download : Partiotion Magic
(power quest partition magic no longer exists, It's acquired by Norton, But you can downlad power quest from other sources. Just google it !)
Search the web safely with McAfee Site Advisor
It tests Web sites for spyware, spam, viruses and phishing so you can click with confidence.
SiteAdvisor's automated robots tests every Web site, download, and e-mail sign-up form on the Web.Web sites are tested for 'phishing' and other online scams, affiliations with dangerous sites, excessive pop-ups, and browser exploits.
and it tells Us:
- Is it safe to use?
- Is it safe to download?
- Is it safe to submit e-mail or other data ?
- What do others say about the site ?
- and shows the more details.
Convert all your media files to any format with Format Factory

Now you can convert all your media files to other media formats using Format Factory.
Format Factory is a must have tool on your windows desktop.
Functions of Format Factory Media Converter
All to MP4/3GP/MPG/AVI/WMV/FLV/SWF.
All to MP3/WMA/AMR/OGG/AAC/WAV.
All to JPG/BMP/PNG/TIF/ICO/GIF/TGA.
Rip DVD to video file , Rip Music CD to audio file.
MP4 files support iPod/iPhone/PSP/BlackBerry format.
Source files support RMVB.
Also it can do some other features like..
Handling damaged media files
Reducing multimedia file types
Picture converting and formatting
You also will love to it's handy GUI features.
Format Factory is a 100% Freeware and No any malwares.
Format Factory Home Page
Download Format Factory
Export Your Blogspot blog to Wordpress
Now Blogger or Blogspot allows users the ability to export all contents of their blog, the Data Liberation team would like to announce the Google Blog Converters project. This new Open Source project provides the ability to easily move blog posts and comments from service to service. This initial release provides Python libraries and runnable scripts that convert between the export formats of Blogger, LiveJournal, MovableType, and WordPress.
For more info.
Blog converter Home
Download Google blog converter here.
Sometimes neither blogspot nor Wordpress will do....
There are a myriad of website hosting options available and each has
it's own distinct advantages. Do your homework and identify your needs in advance
1.2.09
Optimize and Free up your RAM
The new version (1.5)introduces Global Memory Compression technology, which frees additional RAM instantly, at no cost to system performance; process memory reporting; advanced memory configuration options; customizable program sounds; and miscellaneous features and fixes.
Includes automatic memory monitoring and optimization; advanced tray support; fast, threaded freeing with a stop option; multiple system-metric monitors; a simple and attractive GUI; memory reporting and diagnostic logging; and real-time memory information.
It's freeware and nothing to lost you.
Download Free Ram XP Pro
How to Remove virtumonde completely from your computer
Virtumonde :
This virus is reported to record your keystrokes and randomly displays advertisements. This virtumonde.c Trojan will create a DLL (Dynamic Link Library) to facilitate the recording of your keystrokes and communicates with a website located on the internet.
Virtumonde.C attaches to explorer.exe, goes memory resident and verifies that it's running (the virus that is). If for some reason Virtumonde.c is stopped, the memory resident program will fire it back up.
The virus also writes to cookies on the infected computer and may visit more than one internet site. The part that makes VirtuMonde.c tricky is that it's a memory resident and writes to a file that spyware removal programs can't erase.
How I removed Virtumonde Completely from My System
Then I tried Spyware Doctor and it also removed only some parts of virtumonde.
Finally I take up with the Spybot. Spybot Search and Destroy scans the computer and removes the parts left by kaspersky and Spyware Doctor.
So what all you have to do is.
1. Download latest virus scanners like Kaspersky Internet Security, PC tool's Spyware Doctor and Spybot Search and Destroy ( with latest updates ).
2. Now Disconnect the computer from internet and other network connections.
3. Then scan the system first with Kaspersky then with Spyware Doctor and finally with Spybot. (It is now said that Spybot can completely remove all variations of Virtumonde trojan from an infected system)
1. Know more about virtumonde and removal - go here
2. Wikipedia Article on Virtumonde
3. Windows live one care scan
